At the same time, we have two different QR code issues that affect Android and iOS devices. In the case of Android is malware, while in iOS is a bug. Yesterday was made known that iOS has one more bug and this time something that can lead the user to fall into a malicious scheme. As we saw yesterday in detail, iOS, with the arrival of the iOS 11 version, has brought the user a small and interesting increase in the camera app. Since then it has become possible to (natively) read a QR code without the need to resort to third-party apps. However, German website Infosec has found that this feature can be used by cybercriminals to conduct attacks, since reading a QR code displays the information of a site, but the user can be redirected to another site (for example, a website with malware).
As we are currently referring to, not innocently, we have two different QR code issues that affect Android and iOS devices. If in the case of iOS is a bug of the operating system itself, already in the case of Android is even malware in some applications. Who refers to it is the security company SophosLabs, which discovered some applications for Android with malware and were available in the Play Store. These applications hide malware with features to read QR codes and other actions that are deceptive to the user. While this is not the first case of malware-infected apps within the Google Play Store, the Andr/HiddnAd-AJ malware hidden in these applications is designed to look like an Android programming library. In this way, they managed to deceive the Google filtering system. In addition, these applications do not reveal their true intentions until six hours after installation. After that, they start flooding devices with ads. The tech giant Google has already removed these applications with malware, at least those that were pointed out, but for an idea, while they were exposed in the Play Store, they were downloaded more than 500,000 times. The deception used by programmers to fool Google’s “Play Protect” system seems surprisingly simple. First, the apps were, at least superficially, what they actually claimed to be: six were QR code reading applications and one was the so-called “smart compass.” In other words, if you were just testing apps for fun, or for some other reason, you’d be inclined to judge them by its own descriptions. Second, criminals did not immediately activate the adware part of their apps, hiding themselves innocently for a few hours before triggering a barrage of ads. Third, the adware part of each app has been incorporated, at first glance, as a standard Android programming library that has been embedded in the software.
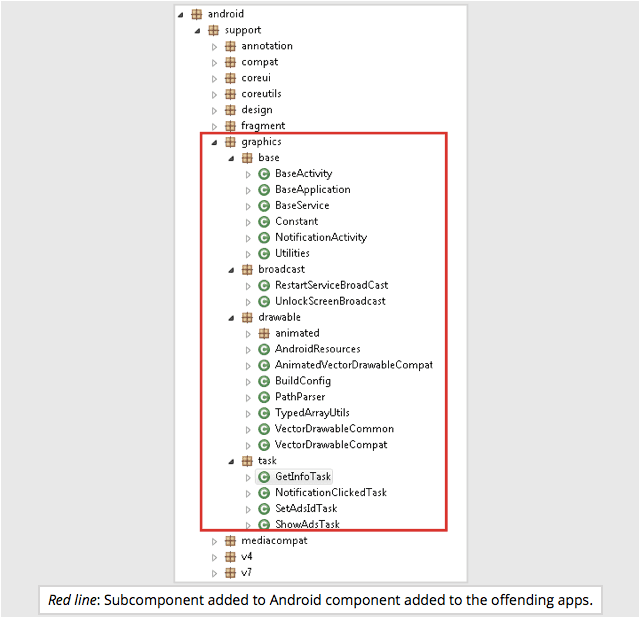
By adding an innocent-looking “graphics” subcomponent to a collection of programming routines you’d expect to find in a standard Android app, the adware engine within the application is effectively camouflaged. For all its apparent innocence, however, this malware does not only display web advertising pages but can also send Android notifications, including clickable links, to entice you to generate advertising revenue for criminals. So, what do you think about this? Simply share all your views and thoughts in the comment section below.